Monitoring the Monitor: How CPUID's HWMonitor Supply Chain Was Hijacked to Deploy STX RAT
Summary/Title Text
Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua. Ut enim ad minim veniam, quis nostrud exercitation ullamco.
Key Findings
The Howler Cell Threat Research Team has identified the following key characteristics of this supply chain attack:
- Supply Chain Compromise: The official CPUID download page for HWMonitor was hijacked to serve a trojanized installer from attacker-controlled Cloudflare R2 infrastructure. CPU-Z was similarly compromised. CPUID confirmed a secondary API was breached for approximately six hours before remediation.
- Massive Exposure Surface: CPU-Z alone has tens of millions of users globally. HWMonitor is the standard hardware monitoring tool used by IT professionals, system administrators, data center operators, OEM hardware vendors, overclockers, and PC builders worldwide. A six-hour window on software of this reach represents extraordinary infection potential.
- DLL Sideloading via cryptbase.dll: A malicious cryptbase.dll was placed alongside the legitimate application. When HWMonitor_x64.exe executed, it sideloaded the rogue DLL via Windows DLL search order hijacking. Only the 64-bit version is affected.
- Five-Stage In-Memory Unpacking Chain: The malware executes entirely in memory across five stages using reflective PE loading, XOR decryption, and layered bitwise transformations. No intermediate payloads are written to disk, significantly hindering forensic recovery and evading signature-based detection.
- Final Payload Attributed to STX RAT: The Stage 5 payload hash matches STX RAT, a remote access trojan with infostealer capabilities previously distributed via a fraudulent FileZilla installer. This links the CPUID campaign to a broader ongoing operation.
- Multi-Campaign Infrastructure: Four distinct campaign tags (tbs, tbs2, tbs3, snip) and referrer fields (CPZ for CPU-Z, monitor3 for HWMonitor) were identified in the C2 callback metadata, indicating an active, segmented operation across multiple software targets.
Summary
The Howler Cell Threat Research Team has identified a supply chain compromise involving HWMonitor, a widely used hardware monitoring application developed by CPUID. The legitimate software download page was compromised and redirected users to a trojanized installer hosted on attacker-controlled Cloudflare R2 infrastructure. The investigation also confirmed that CPU-Z, another CPUID product, was similarly affected.
How the attack worked
- The malicious installer contained an additional DLL, cryptbase.dll, placed alongside the legitimate application and sideloaded when the 64-bit version of HWMonitor executed.
- This triggered a multistage malware chain using reflective PE loading, XOR decryption, and layered bitwise transformations across five stages, all executed entirely in memory.
- The final payload, identified as STX RAT, contacted the hardcoded C2 domain welcome[.]supp0v3[.]com and transmitted host metadata for victim identification and campaign tracking.
Why the scale of this attack matters
CPUID's tools are not niche utilities; they are the de facto standard for hardware diagnostics across the global technology community. CPU-Z alone has tens of millions of users worldwide. HWMonitor's core user base includes:
- IT professionals and system administrators conducting diagnostics
- Data center engineers validating server thermals
- OEM hardware vendors qualifying new components
- Security researchers running forensic workstations
- Corporate IT departments managing device fleets
The portable (ZIP) version is routinely carried on USB drives and run directly on production machines without installation, reaching environments that block installer-based software. This is not an attack that happened to hit a popular tool. It was almost certainly designed to target exactly this user base. Compromising the CPUID download page is a direct attack on the people most likely to have administrative access, deep system visibility, and credentials worth stealing.
What a successful infection delivers to the threat actor
- Browser credentials and session cookies capable of bypassing MFA
- Persistent remote access via the STX RAT component
- Crypto wallet keys and password manager data
- VPN and FTP credentials enabling lateral movement into enterprise networks
- Victim profile data segmented by campaign tag and referrer software, enabling prioritized follow-on exploitation
A six-hour compromise window on software of this reach represents an infection opportunity that most targeted campaigns never achieve.
Campaign Timeline
- Initial Discovery, April 9, 2026: A Reddit post surfaced raising concerns about potential malware distributed through recent versions of HWMonitor, prompting community discussion and preliminary VirusTotal analysis.
- Compromise Identified: The legitimate CPUID download page (hxxps[://]www[.]cpuid[.]com/softwares/hwmonitor[.]html) was found redirecting users to a malicious package hosted on a Cloudflare R2 bucket.
- Trojanized Package Distributed: Users downloading HWMonitor v1.63 received a compromised archive containing a malicious cryptbase.dll alongside otherwise legitimate components.
- DLL Sideloading and Payload Execution: Upon launching HWMonitor_x64.exe, the malicious DLL was sideloaded, initiating a multi-stage unpacking chain that deployed STX RAT entirely in memory.
- C2 Communication Established: The malware transmitted JSON-formatted victim metadata to the hardcoded C2 server (welcome[.]supp0v3[.]com) for campaign tracking and victim profiling.
- Vendor Acknowledgment (April 9-10): CPUID author Samuel Demeulemeester publicly acknowledged the compromise, confirming that a secondary API was breached for approximately six hours, causing the main website to randomly serve malicious download links. The signed original files were not compromised; the breach has since been remediated.
- Attribution and Correlation: The final payload hash correlates with prior reporting linking it to STX RAT campaigns previously distributed via a fraudulent FileZilla installer.
Technical Analysis
HWMonitor is a widely used hardware monitoring utility that tracks system temperatures, voltages, and fan speeds. Howler Cell began its analysis after a Reddit post surfaced reporting suspected malware distributed through recent versions of HWMonitor.
Through a combination of community discussion (Figure 1), VirusTotal analysis (Figure 2), and official confirmation from CPUID (Figure 3), it was determined that the legitimate download page had been compromised to redirect users to a malicious package hosted on a Cloudflare R2 server. The full URL of the malicious payload is provided below:
hxxp[://]pub-fd67c956bf8548b7b2cc23bb3774ff0c[.]r2[.]dev/hwmonitor_1[.]63[.]zip
Figure 1: Reddit post
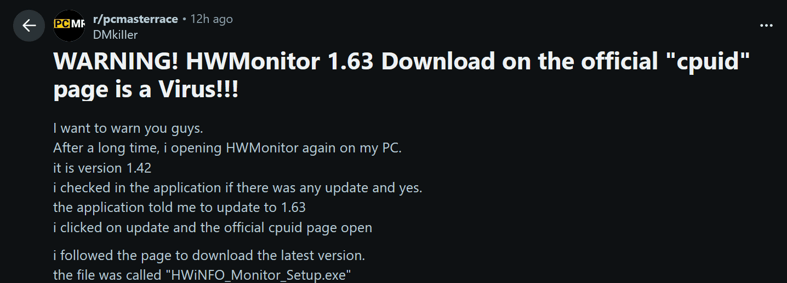
Figure 2: VirusTotal Lookup
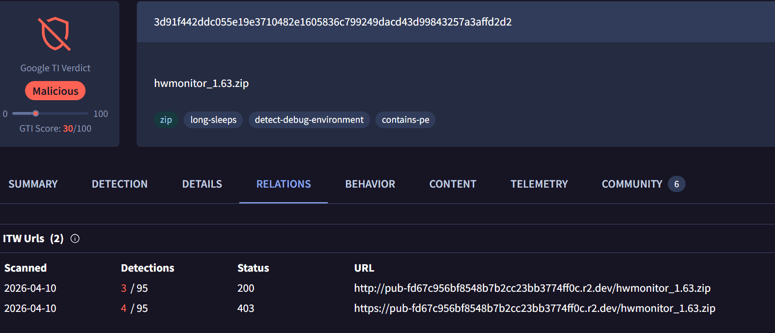
Figure 3: Vendor's post on X
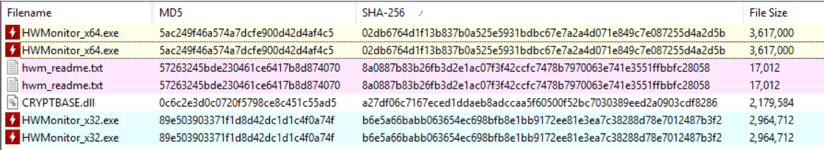
Upon inspection, the compromised package was found to contain an additional DLL named cryptbase.dll, while all other components appeared legitimate and consistent with the original distribution version 1.63 (see Figures 4 and 5).
Figure 4: Compromised package containing malicious DLL compared to legitimate package v1.63
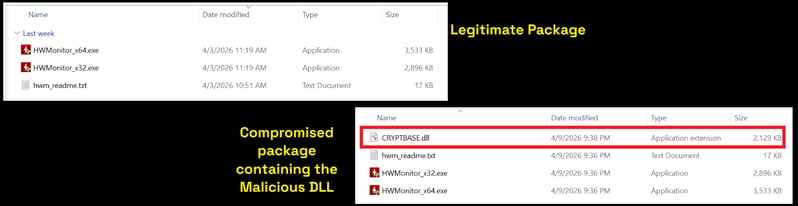
Figure 5: Hash check on legitimate and compromised packages
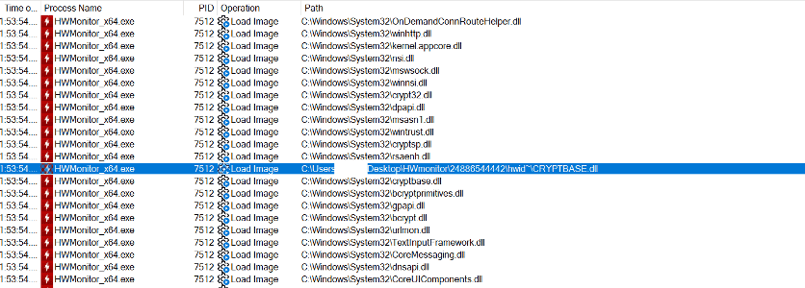
Upon execution of HWMonitor_x64.exe, the malicious DLL is sideloaded into the process, as evidenced by the Procmon logs captured in Figure 6, triggering the execution of its DllMain entry point. Since the malware relies on DLL search order hijacking, only the 64-bit version of HWMonitor is affected in this attack.
Figure 6: Malicious DLL loaded by HWMonitor_x64.exe
Cryptbase Analysis
The Cyderes Howler Cell Threat Research Team conducted a technical analysis of the malicious component, cryptbase.dll. The file is a 64-bit DLL module with a timestomped compilation timestamp set to 2077-08-31 05:16:43.
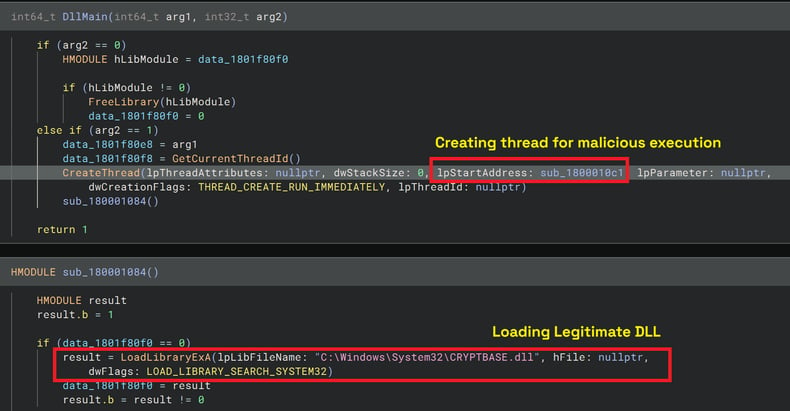
Upon execution within DllMain, the malware spawns a separate thread, which initiates an additional thread responsible for executing the primary malicious payload. This multi-threaded approach is likely employed to release the loader lock. Concurrently, the malware loads the legitimate cryptbase.dll from the System32 directory (Figure 7) and returns TRUE to prevent a deadlock condition.
Figure 7: DllMain thread creation and legitimate module load
Upon execution, the malware sends JSON-formatted metadata (Table 1) to the hardcoded C2 server (welcome[.]supp0v3[.]com), likely for tracking and profiling campaign victims with campaign ID "tbs." The callback URL registers infected victims as shown in Figure 8. Analysis identified four active campaigns tagged tbs, tbs2, tbs3, and snip. Concurrently, it unpacks a second-stage payload in memory (Figure 9), consisting of a compact shellcode stub designed to execute the reflective PE loader. The referrer field identifies the targeted software package: CPZ for CPU-Z and monitor3 for HWMonitor.
Figure 8: Callback to register victim
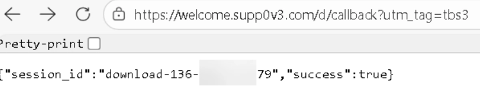
Table 1: JSON Metadata Sent to C2
| tag | "tbs" |
| referrer | "monitor3" |
| callback | hxxps[://]welcome[.]supp0v3[.]com/d/callback |
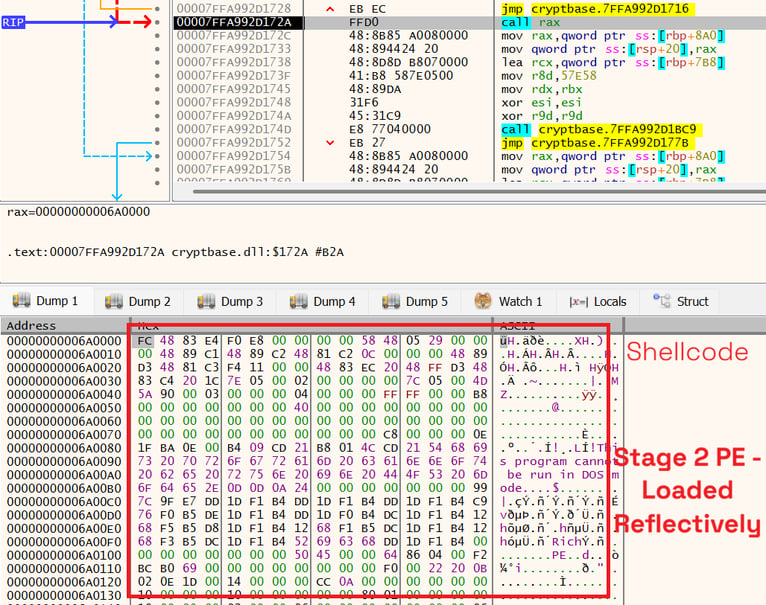
Figure 10: Stage 3 unpacked in memory
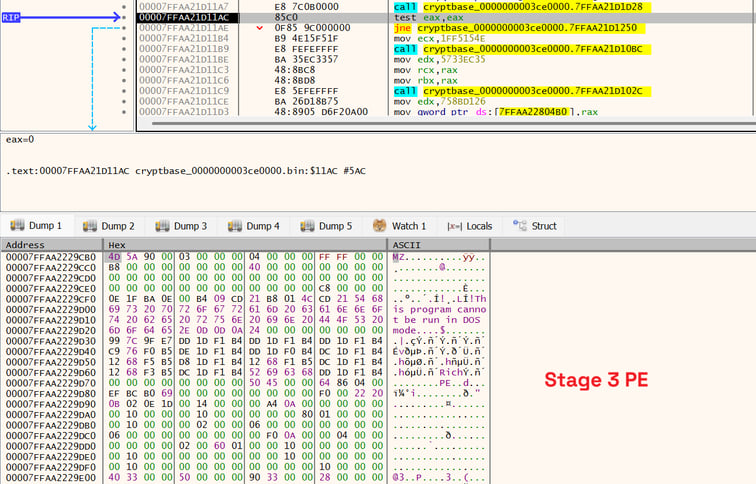
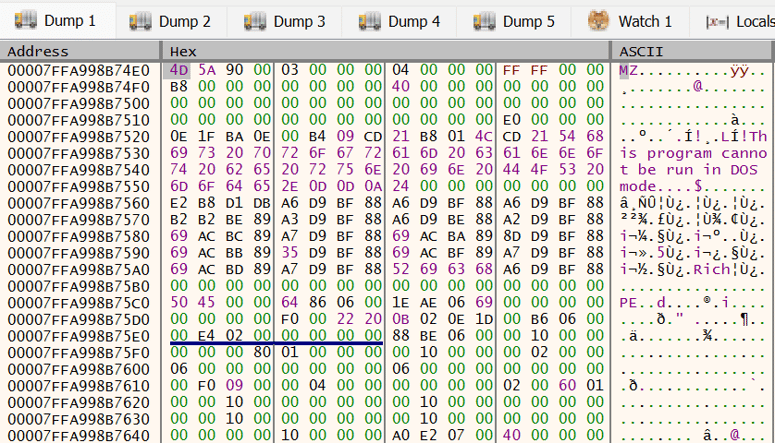
Stage 3 follows a similar pattern, functioning as a reflectively loaded DLL. Once mapped and executed, it unpacks a Stage 4 PE in memory using the same XOR decryption and bitwise manipulation routine to extract the fifth and final stage (Figure 11). This final payload is the core malware binary, identified by SHA-256 hash:
52862b538459c8faaf89cf2b5d79c2f0030f79f80a68f93d65ec91f046f05be6
This hash has been attributed to STX RAT, a malware variant previously observed being distributed through trojanized FileZilla installers.
Figure 11: Unpacked RAT in memory - STX RAT
What Should Defenders Do?
- Verify HWMonitor v1.63 installations: Compare file hashes against the known IOCs listed in this report. If a match is found, isolate the affected system immediately and initiate incident response procedures.
- Block the identified C2 domain and malicious URL: Add welcome[.]supp0v3[.]com and the Cloudflare R2 URL to DNS, proxy, and firewall blocklists at the network perimeter.
- Scan for cryptbase.dll outside System32: Any instance of cryptbase.dll present in application directories, particularly HWMonitor installation folders, should be treated as an immediate indicator of compromise.
- Review credentials and session tokens on affected systems: STX RAT carries credential theft and session cookie harvesting capabilities. Force password resets and revoke active sessions where compromise is suspected. Prioritize accounts with administrative or privileged access.
- Enforce hash validation for third-party tools: Establish a process for validating SHA-256 hashes on all downloaded utilities before execution, particularly portable tools run directly from USB or network shares.
- Alert IT and security staff specifically: Given that HWMonitor's core user base is IT professionals, system administrators, and security practitioners, proactively notify these groups and treat any machine in this user population that ran a CPUID download between April 9-10 as potentially compromised until verified.
Conclusion
This analysis documents a sophisticated supply chain attack that weaponized the trust and popularity of HWMonitor to distribute STX RAT. The threat actor compromised the official CPUID download page to serve a trojanized package, employing DLL sideloading as the initial execution vector followed by a layered, five-stage in-memory unpacking chain designed to evade detection. The use of a timestomped compilation timestamp, reflective PE loading, and exclusively in-memory payload execution demonstrates a deliberate effort to hinder forensic analysis and bypass traditional security controls.
The attribution of the final payload to STX RAT, previously linked to compromised software distribution sites, suggests an ongoing campaign by a threat actor with a consistent operational playbook built around abusing trusted software channels. The identification of four active campaign tags and multiple referrer values confirms that this infrastructure is actively maintained and specifically targeting CPUID's user base by product.
The CPUID compromise reinforces a broader trend: commodity utilities with technically sophisticated, high-privilege user bases are increasingly attractive supply chain targets. An IT administrator or security engineer running HWMonitor on a production machine is a far higher-value target than a typical consumer endpoint. Defenders should treat any cryptbase.dll present outside of System32 as an immediate indicator of compromise, enforce hash validation on third-party software downloads, and monitor endpoints for the C2 and file IOCs listed in the Appendix. Detailed remediation steps are provided in the What Should Defenders Do section.
Appendix
Indicators of Compromise (IOCs)
|
Name |
SHA-256 |
|
HWMonitor_x64.exe (Legitimate -- abused for DLL sideloading) |
02db6764d1f13b837b0a525e5931bdbc67e7a2a4d071e849c7e087255d4a2d5b |
|
cryptbase.dll (On-disk) |
a27df06c7167eced1ddaeb8adccaa5f60500f52bc7030389eed2a0903cdf8286 |
|
Stage 2 (In-memory PE) |
1331f19c6732fca81f32c4cec9f89abf26371ed9d3665954f491c89e2c55e5bb |
|
Stage 3 (In-memory PE) |
116d806a5ca6f34fdd04061499daca9a352feb2e3f291c7ef3e5d470fe875f7f |
|
Stage 4 (In-memory PE) |
a70645f46eee6d765c54ba4a5c48166bd83bcfbc7771a82be9ed48ab4871ebfa |
|
Stage 5 -- STX RAT |
52862b538459c8faaf89cf2b5d79c2f0030f79f80a68f93d65ec91f046f05be6 |
C2 Infrastructure
URL: hxxps[://]welcome[.]supp0v3[.]com/d/callback
Domain: welcome[.]supp0v3[.]com
MITRE ATT&CK
| Tactic | Technique |
|
Initial Access |
T1195.002 -- Compromise Software Supply Chain T1204.002 -- User Execution: Malicious File |
|
Execution |
T1106 -- Native API |
|
Defense Evasion |
T1574.002 -- Hijack Execution Flow: DLL Side-Loading T1027.002 -- Obfuscated Files or Information: Software Packing T1620 -- Reflective Code Loading T1140 -- Deobfuscate/Decode Files or Information T1070.006 -- Indicator Removal: Timestomp |
|
Discovery |
T1082 -- System Information Discovery |
|
Command & Control |
T1071.001 -- Web Protocols T1105 -- Ingress Tool Transfer |
|
Credential Access |
T1555 -- Credentials from Password Stores T1539 -- Steal Web Session Cookie |
|
Exfiltration |
T1041 -- Exfiltration Over C2 Channel |
|
Collection |
T1005 -- Data from Local System |
References
Stay informed with Howler Cell
Receive the latest Howler Cell news and research directly to your inbox.

Optional featured resource text
Howler Cell has been tracking and investigating the new variant of MedusaLocker. MedusaLocker is a well-known ransomware family active since late 2019
Ready to close your security gaps?
To stay ahead of today’s relentless threatscape, you’ve got to close the gap between security strategy and execution. Cyderes helps you act fast, stay focused, and move your business forward.